Vesta on Twitter: "𝐕𝐒𝐓'𝐬 𝐩𝐞𝐫𝐟𝐨𝐫𝐦𝐚𝐧𝐜𝐞 𝐝𝐮𝐫𝐢𝐧𝐠 𝐔𝐒𝐃𝐂 𝐝𝐞𝐩𝐞𝐠 The recent $USDC depegging has further highlighted the 𝐜𝐫𝐮𝐜𝐢𝐚𝐥 𝐧𝐞𝐞𝐝 for a decentralized and resilient stablecoin. Let's analyze VST's peg protection ...
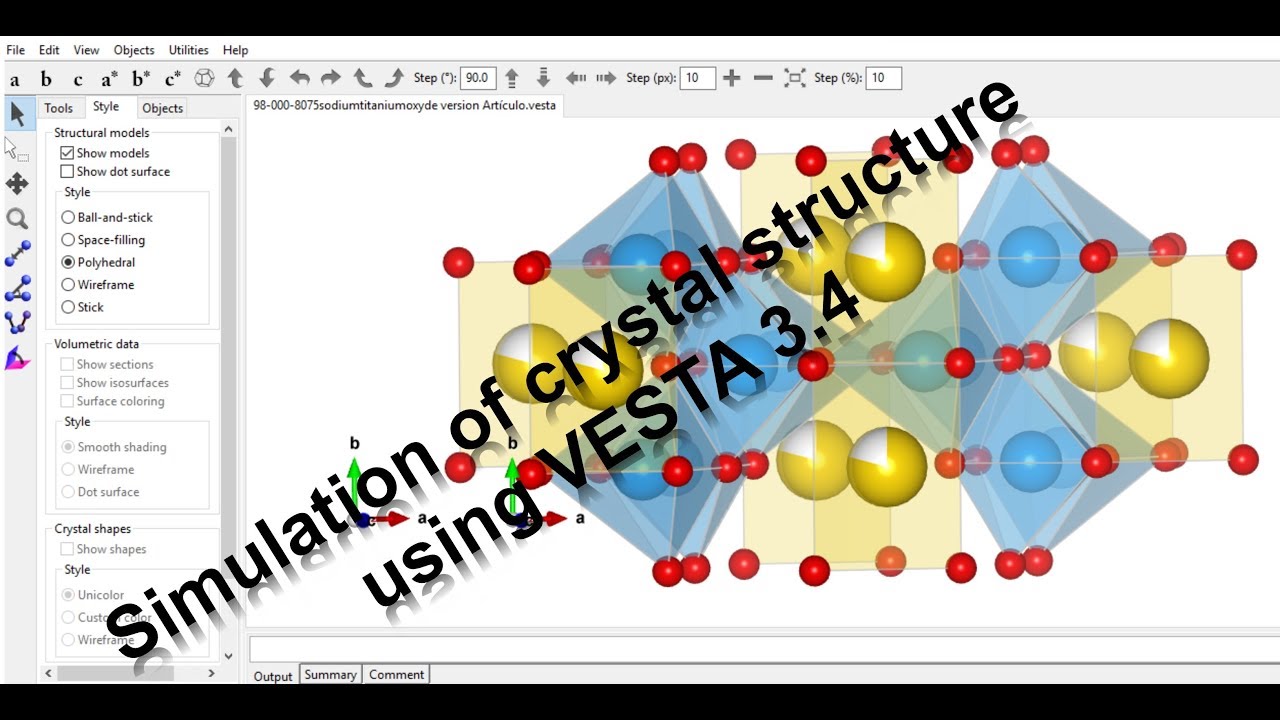
![PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c572e58b9dd4abf559046fc4ce42a7c42df4ba34/82-Figure10.3-1.png)
PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar

An overview of Vesta, a platform which primarily consists of a smart... | Download Scientific Diagram
![PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c572e58b9dd4abf559046fc4ce42a7c42df4ba34/16-Figure2.1-1.png)
PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar
CORPORACIÓN INMOBILIARIA VESTA, S.A.B. DE C.V. : VESTA * Stock Price | MX01VE0M0003 | MarketScreener

MOR zeolite crystal structure drawn by VESTA. Analysis was conducted by... | Download Scientific Diagram
![PDF] Spacecraft dynamic analysis and correlation with test results : Shock environment analysis of LISA Pathfinder at VESTA test bed | Semantic Scholar PDF] Spacecraft dynamic analysis and correlation with test results : Shock environment analysis of LISA Pathfinder at VESTA test bed | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/0d0fdb650c0d8ef958afc5f8c3711b94a43276a1/12-Figure2-1-1.png)
PDF] Spacecraft dynamic analysis and correlation with test results : Shock environment analysis of LISA Pathfinder at VESTA test bed | Semantic Scholar

GitHub - kvesta/vesta: A static analysis of vulnerabilities, Docker and Kubernetes cluster configuration detect toolkit based on the real penetration of cloud computing
![PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c572e58b9dd4abf559046fc4ce42a7c42df4ba34/81-Figure10.2-1.png)
PDF] VESTA: a three-dimensional visualization system for electronic and structural analysis | Semantic Scholar

Kúpiť Ultra ľahký nadol vesta bez rukávov pre mužov turtleneck jeseň zimná bunda ženy ľahký vetru prenosné prešívaná vesta ~ Bundy & Coats / www.pumask.sk